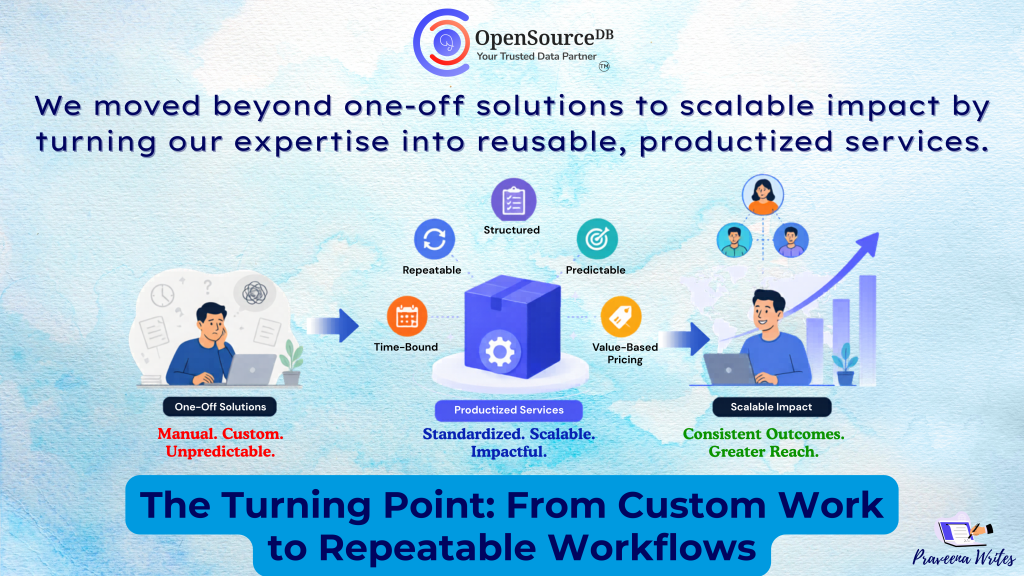
We Productized Our Services with AI: Pricing Lessons We Learned
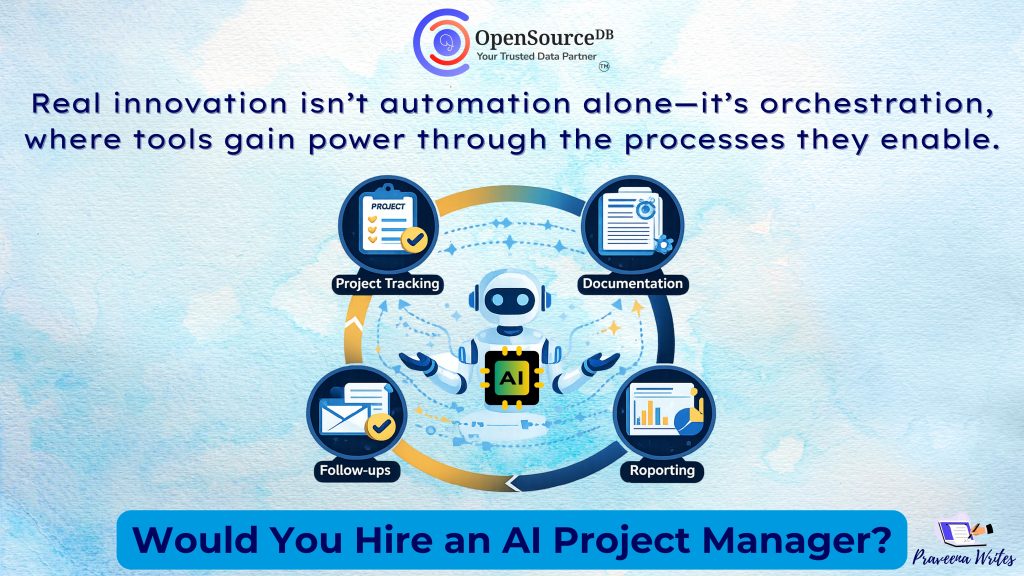
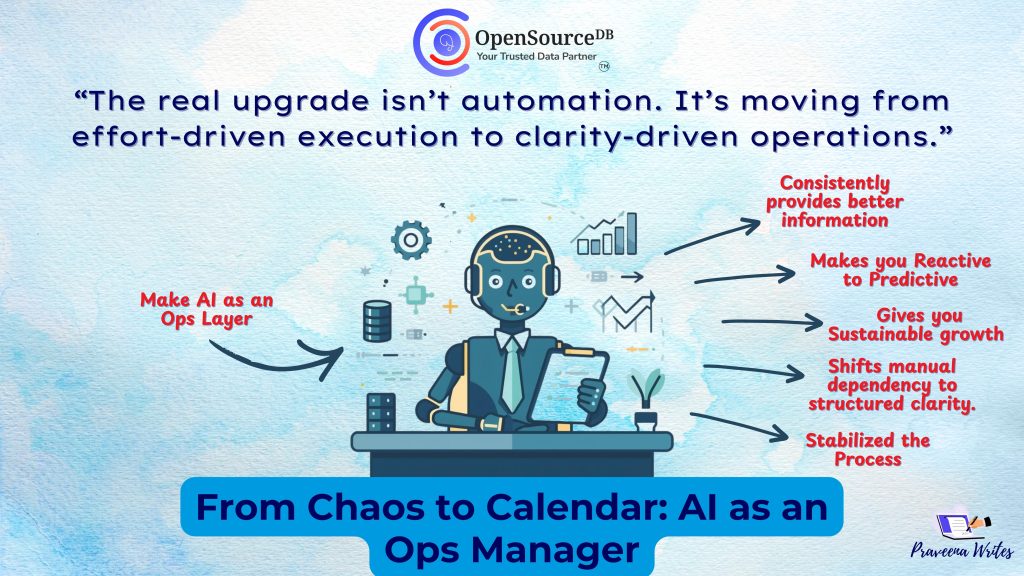
For years, service businesses operated on a familiar model: time, effort, and people. More hours often meant more revenue. More […]
We Productized Our Services with AI: Pricing Lessons We Learned Read Post »